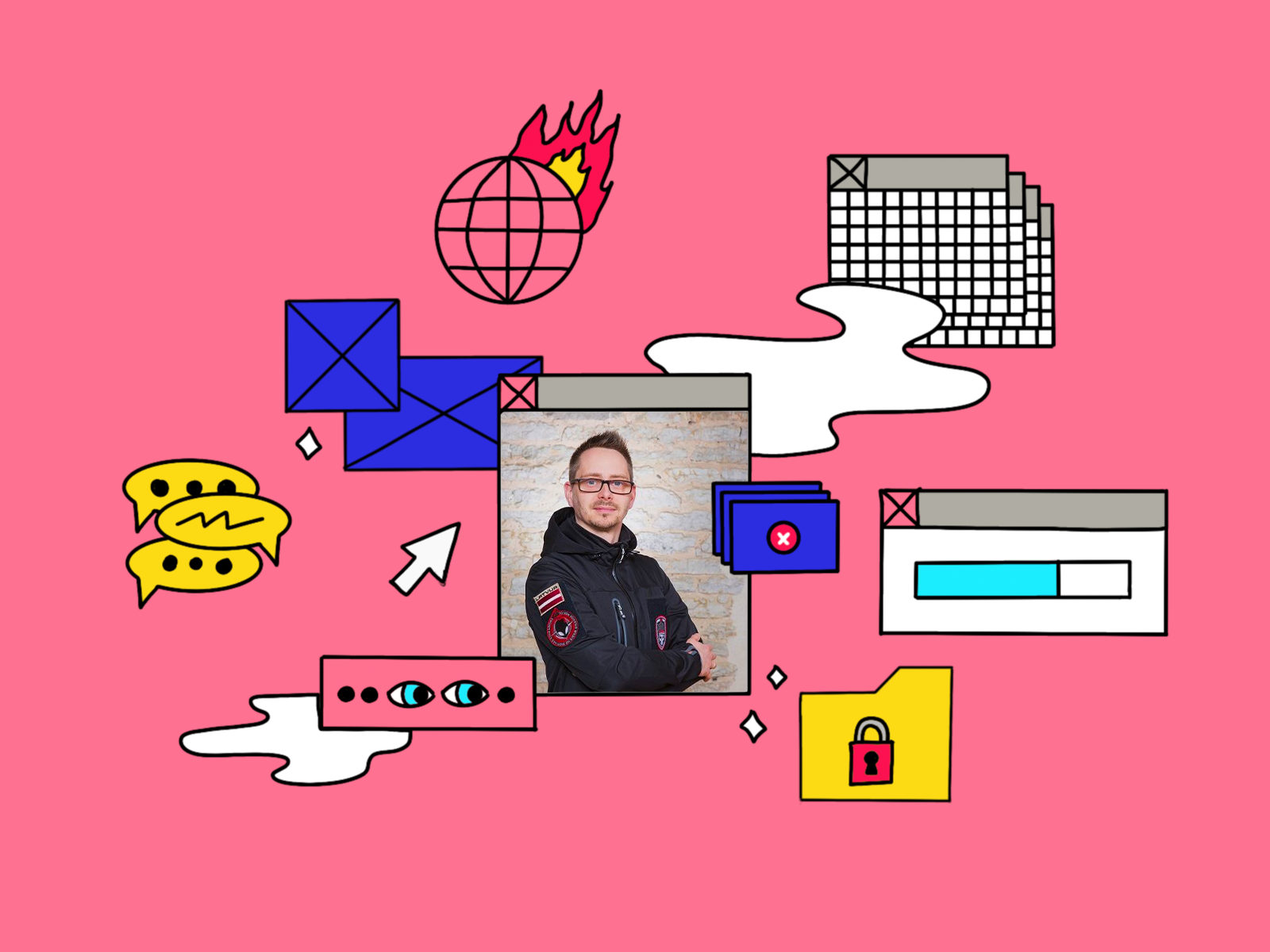
Historical cyber-attack against Latvia, e-voting system in Estonia, cyber mayhem scenarios and everyday practice of cyber-security during our everyday’s life. Interview with Dr. Bernhards Blumbergs, leading security expert from the Baltics.
At the beginning of July, a historical cyber-attack occurred against Latvia by pro-Russian hackers. From an ordinary point of view, how does a big cyber-attack look like? How can you capture the moment when you realize that it is going on as sometimes 3-4 years can pass before the realization that system has been breached?
Being targeted by hacktivist organizations or spin-offs is not anything uncommon, not unusual. However, I would rather be more precise that not in July, but at the beginning of the May we saw the spike of call for hacktivism on the Telegram channels when similar initiatives like Killnet and others alike would be spinning up. This was primarily sparked not only by the Russian aggression in Ukraine, but because the Latvian government decided to dismantle one of the occupation monuments here, which raised huge debates and physical protests, which we retaliated also in the cyberspace. If we look at the Killnet and alike, they are definitely a low sophistication attacks which focus on recruiting any ordinary citizens or like-minded people to engage in. Low sophistication acts would constitute to the ones, such as, automatically searching for the vulnerabilities and using already available tools online just to exploit those vulnerabilities or purchasing a distributed denial of service attack package. These actions are very low tech, using whatever is available, just scanning something and seeing if it breaks. We were one of the nations that got hit by this wave of attacks, but afterwards, in upcoming months, Lithuania also got hit by similar activities due to the Kaliningrad standoff. If I look at Killnet and other likeminded hacktivist groups, there was an initial lack of coordination, and they were missing the context to perform target acquisition and conduct their attacks. They were hitting unrelated targets without even understanding what those are and what is their role in our national security or government ecosystem. Where I mentioned lack of context, it is because they clearly use the acronyms used in Russian language and they would look for similar domain names or websites that would correspond to those acronyms, but in our language those acronyms would mean something totally different, therefore they would aim for a certain target, but essentially would hit something else. That is what adds to their low sophistication, lack of coordination and absence of knowledge. Any 12-year-old kid can follow instructions, click on a link, download a piece of software and be part of a distributed denial of service attack or just run an automated attack without even knowing what that means.
The other part is about detection. How fast can we detect?
I would like to split that into different operations: overt and covert operations. Overt operations, which are open operations like Killnet, where you hit a button and the attack is being launched, you can detect right away. This is like an elephant walking into a room, you would notice that. The covert operations, which are clandestine or hidden operations, are mostly related to government organizations or government affiliated organizations, those would follow a more distinct patterns of being more persistent and going for a long-term effect and being stealthier. How do you detect those? That is really tricky for sure. On an average they can be there for a few months and spanning up to years. That is really on how the incident response works or if an attacker makes a mistake. If an attacker makes a mistake, then incident response team may proceed and investigate what has caused this suspicious activity. What can decrease this response and detection time is doing a proactive threat hunting operations, meaning that I assume that my network or my organization has been already attacked and breached. To perform a threat hunting operation requires the assembly of a team of experts and instruct them, that their task is to look in organization’s network and try to find any traces of past or ongoing adversarial activities. We don’t know if the adversary is there in our network but look for anything that is suspicious and if this operation is successful in finding a threat or in identifying that there is no threat actor, we may already respond to such events. Threat hunting actions are very specific and require primarily skilled human resources, human experts are the key on identifying, assessing and evaluating threats – this is not primarily related to the use of technology. Technology does play a role; however, a human mind and human expertise is the one that is very critical in responding or identifying adversary in your network. It’s like if there is an uninvited guest hiding somewhere in your flat, you would be trying to open all the shelves, and search in various locations to look for any traces left by that uninvited guest. If the adversary is very good at hiding, you might not find it directly, but there might be some traces left behind.

You mentioned the human factor. How much does it cost for a company to detect, to track, to build a system that can resist the attacks coming from the cyber space. Is it an increasing or decreasing cost for the companies like banks that have headquarters in Riga?
The cost for sure is significant in investing this capability. However, what is the cost on not investing in this capability? And I can’t tell you about the numbers, however, if the cost on investing to protect is less than losing your business and sometimes going out of the business because losing credibility and losing assets, you should definitely invest in consistent incident response capability augmented by threat hunting operation surges. However, this is mostly an investment from the management side and the right security-focused mindset has to be groomed and facilitated. Firstly, understanding the requirement for this: the management won’t always understand, because they’re looking for business profit, they want to have the business to be as profitable as possible, hence neglecting or minimizing investments into protecting their business operations from cyberattacks. In your question you also mentioned banks, who are a bit of a different breed because for them to operate here in Europe and globally, they have to comply with strict European, international and national standards, which means that they are obliged to ensure and maintain the highest possible level of security. But that doesn’t apply to a regular company. If you are a viable target, either direct or indirect you may still be attacked. Maybe you are working with a customer that is the intended target for an attacker. And you would be used as a collateral damage within supply-chain integrity abuse or a pivot point to go through you because you know or have something, that is of a value to the attacker and may help them to achieve their goals. You may never know about this but doing a proper threat landscape assessment and evaluating the risks of not investing and potentially going out of business is something of a concern here.
We talked about the cyber-attack conducted by Killnet. We can see that in the cyber space, the situation has changed since the 24th of February. The experts stated a few years ago that the Third World War is going on in the cyber space, for me it was more like a big title in the newspapers than true. From your point of view, how would you assess the situation right now? What changed since the war started and how did the situation look like before the war?
The question maybe is on some of the people’s minds – has World War II actually ended, right? Maybe this is just an extension of that, but let’s not jump into that topic. What happened on 24th of February is that everyone was expecting that there was a huge buildup in cyberspace that might turn out into a global cyber mayhem. We saw that the Russian Federation was laying ground by trying to impede the capabilities of Ukrainian government and organizations, and nearly everyone was thinking about being on a brink of a huge cyber war, something you might have seen in Hollywood movies. However, the situation of history has proven us otherwise. Nothing of those cyber mayhem scenarios happened. Actually, nothing significant happened as the conventional forces were deployed as a primary choice for the conduct of the warfare. I’ll talk later about what cyber war means and if we have ever experienced it or if we will experience a cyber war in near future. For now, I can say that the word “cyberwar” has been mostly being abused as a buzzword to draw attention. What happened on 24th of February, when the Russian invasion started, is that it felt like it was gloves-off for everyone globally. It doesn’t matter if you were a government or non-government entity, it sparked a lot of uncontrolled global initiatives throughout the cyberspace. For an example, there was an upsurge in the formations of hacktivist groups to conduct attacks against engaged countries and their allies to have an impact on their capabilities or just hacking for fun. However, these have not led to the destruction of infrastructures or spreading terror through the cyberspace. I can’t tell you that no, there has been no destructive activities through cyberspace which would be comparable to the destruction and terror delivered by the conventional means. If we consider the terminology, war commonly implies that there is significant damage to infrastructure, debilitation of vital services, casualties, and other harsh effects due to the conduct of the warfare. This has not happened within or through the use of cyberspace. People are not dying from the attacks in cyberspace. People are dying from the bullets and shelling that are shot in the actual physical space. Now, if we reflect on the previous considerations and look at the ways on how cyber activities and cyber operations are performed within the current conflict, I am quite confident that cyber war is unlikely to happen. However, cyber operations will always be a significant and an ever-increasing component to the conventional warfare and intelligence gathering. This is nothing new and we have already experienced the use of the cyberspace to perform a preparatory work for laying ground or preparing the battlefield, such as, affecting defensive capabilities, that will allow conventional forces to move onwards and achieve their goals by minimizing losses or giving a chance of surprise attack. We’re going to see it even more and more as the technology evolves and our interdependency on it becomes ever intertwined. It doesn’t matter if it is going to be an energy sector, telecommunications, or transportation. The people mostly assume that there will be one button and the country will stop functioning, the power stations will exploded, and so on and so forth. If you have seen the Die Hard 4.0 movie, I would presume everyone was waiting for something similar. Nothing like that happened. Bruce Willis didn’t come in and didn’t save the day. There’s still a day yet to be saved. We are looking for the Bruce Willis out there in cyber space.
I talked with an expert from Canada called Abishur Prakash, a geopolitical futurist. In one of his books dealing with geopolitics and AI, he stated that a new iron curtain will be built in Europe in the terms of the digital space. We will have another payment system in China or Russia than in Europe. UnionPay, Yandex exist, and they are working quite well, Russians don’t use Google at all. How do you comment this analysis?
This is not the first case of digital iron curtain, right? We have China, we have North Korea, and few other nations, which have already placed those restrictions country-wide. Now, Russia is not just pursuing this approach recently, it’s been on their agenda already for at least a decade with goals set towards segregating from the rest of the Internet and trying to control and manage the resources within their own country. If it’s going to happen or not, this is still a question or debatable. For sure a certain level of control and certain level of isolation has been already achieved and it is partially possible by Russian Federation with all the services that they are trying to develop and localize internally. If they’re going to be fully isolated? I would rather say at this point, that in a foreseeable future most likely not, because the countries within the global cyberspace have been so deeply intertwined and interdependent on each other. You mentioned the payment systems and the SWIFT service. The decision to limit and disconnect Russia from the SWIFT payment system resulted in a few countries joining China’s alternative service. For sure, the isolation from global internet is a path that is pursued by like-minded countries, which want to maintain strict control over the national cyber- and information space and exclude other nations to access it. In this case who controls the information? Is that Yandex, Google or any private or public entity? For sure trying to localize and have the information stored or managed within the country just makes sense, many nations world-wide are trying to achieve that to a certain extent, while still maintaining the balance and being part of the global Internet ecosystem.
What about the data sovereignty? Some countries decided that all the data related to their companies, people, government should be based in their own territory.
What’s the difference from the EU GDPR? The European Union clearly states as well that EU citizens’ data should be co-located or located within the physical boundaries of the European Union. Meaning, that even the global companies like Google, Microsoft, or Apple if they store your data in their cloud services, according to the end user license agreement or GDPR compliance, they would be bound to store your data in the data centers physically located in the EU. Now, if that is actually done, this is a question of compliance and verification. This is left to those auditors and supervising bodies to verify this compliance. However, if companies don’t comply with this, they might go out of business or face hefty fines. Data sovereignty for the Russian Federation is something they have been striving for, even with placing restrictions on VPN usage within the Russian network or RUNET. That is already something that implies that data is being stored somewhere, where stricter supervision and controls might be enforced.
If we are talking about the e-state, there is a good example: Estonia. It has e-governance, e-voting and as far as I know the database of the voters was leaked by hackers. What are the advantages and disadvantages of a digital state from a current point of view?
The question here is not what happens if the nation decides to go and digitize. The question here is what if the nation decides and does not digitize. At this era of information, the one who is able to collect and process larger quantities of information in less time will be ahead of others. Not digitizing at this moment is something that will slow down the country’s ability to evolve, compete, and further impede the decision-making process. We are living in the information age, and for the governments to be compliant and be able to provide their services, they must be going hand in hand with digital age. Estonia has been very good on advertising this, because they have had a very solid political decision and direction on promoting this. Maybe they have not always been very good on implementing or designing, but they’ve been very good on doing a very solid public statement campaign. For sure, I can’t neglect that they’ve been in some aspects on a forefront of the digitization of the state, specifically, if we look at the interconnection of various government services into a united digital platform and digitalization of the elections. If Estonia’s e-voting system has previously been actually hacked or not as claimed by posts on social media and few news portals, we don’t know. For sure Russia is engaging in information warfare by trying to oversaturate the information space with fake information. We’ve seen the announcements on social networks and news groups of some sites being hacked or critical databases being breached just by ”Photoshopping” a picture. If the society starts to lose the trust in the system, they will try to avoid using it. Even if that has not been hacked physically, the attacker will have already succeeded by shedding doubts on system trustworthiness. Is conventional ballot voting safer than digital voting or voting by a physical snail-mail? I would say definitely not. Digital voting is not perfect as any other voting or decision-making process doesn’t matter either digital or physical form. It is as flawed as humans who design and manage it. However, the governments to be able to maintain their governance by using the cyber means, they have to have clear understanding on their critical asset protection and deploy alternative methods in case of a failure or unavailability. The government who doesn’t act upon protecting digital assets, their secure design and supervision, and implement their redundancy might be leading towards a disaster.
Could you give us some everyday IT tips and tricks? What should we do to protect our little homes from the spooky hackers?
The first is a reasonably strong password with two factor authentication and the second is being aware and mindful on what you share about yourself on social networks and social media. A strong password is relatively a long password, it is recommended to be a passphrase you would remember. A passphrase can be formed out of any words, such as, anything that you see, an object around you, it might be as simple as saying YesterdayWas ARainyDay. For an attacker to try to guess your password by brute-forcing it character by character would consume more resources the longer you create your password passphrase. Of course, unless your password is being reused or leaked somewhere else. That is where two-factor authentication comes into the play. Two-factor authentication is a second factor, either it is an authentication software on your phone, SMS message, or an alternative method like a hardware NFC tag that you would use to uniquely authenticate against a particular service. When it comes down to the second point, which means that being conscious, aware and mindful about what we share about ourselves on social media directly links to that. Now I don’t want everyone to get into the paranoid state, but a slight grain of paranoia is always healthy. Don’t share your personal information. Don’t make photos of your credit cards or driver’s license. That would directly welcome having your digital identity stolen or somehow being abused. For us to be safe, we need to make sure that our digital twin – we create our digital twins in our digital presence, such as, social media – is protected as well as we are. I’m not walking around on the street and loudly announcing the address, where I live for everyone, right? I don’t want to broadcast this and invite unwelcome guests. Sometimes we just think about the virtual world as something intangible and this psychological perception of digital world varies. For younger generation, they might say that the physical and digital worlds are pretty much the same and no distinct line separates it. Because by having this direct interconnection between those two, they might treat everything that happens to their digital twin in cyberspace as an actual thing in a physical world. Are you an influencer? If you have a social network account, you will be posting a lot of information, you will be drawing attention, not necessarily saying that the information that you post is wrong or irrelevant, but the more you post, the more attention you draw. However, you as a person might not be attacked, but your account that has thousands or maybe millions of followers might be attacked because in modern age it is treated as an asset, which produces profit. This is where my first suggestion is, having strong password phrases with two-factor authentication will help you in the long run to protect your digital assets. We’ve seen influencers or even government representative accounts being hacked and being abused to spread misinformation among the followers. These are the two fundamental things as a part of cyber-hygiene: being aware what you do as a digital twin in social networks, in a digital space, and protecting your identity with a strong password and two-factor authentication.
Dr. Bernhards Blumbergs is a lead cyber-security expert at the Information Technology Security Incident Response Institution of the Republic of Latvia (CERT.LV) and as the former Technology Researcher at the NATO Cooperative Cyber Defence Centre of Excellence (NATO CCDCoE) also the Ambassador of the Centre since 2018. He is the creator and the technical director for the world’s largest and most innovative full-spectrum offensive cyber operation exercise, Crossed Swords. He is a certified exploit researcher and advanced penetration tester (GXPN), and Industrial Cyber Security Professional (GICSP). He has a strong military background, targeted at developing, administering and securing wide area information systems. Dr. Blumbergs received his Computer Science PhD degree in Cyber Security from Tallinn Technical University in 2019, with his dissertation being on specialized cyber red team responsive computer network operations.

Niklas Paschburg: The alchemist of sounds

A mixture of Japanese minimalism and street food: introducing CUDO